Microsoft has confirmed that the company complied with a request from the United States Federal Bureau of Investigation to provide BitLocker encryption recovery keys for unlocking customer data on three laptops. According to the report, early last year the FBI handed a warrant to Microsoft for recovery keys that were protecting three laptops from the Guam area, which were running Microsoft’s BitLocker encryption on their drives. The article explains that BitLocker uses 128 and 256-bit AES encryption over entire drive volumes, so the data becomes unusable once it is out of the user’s hands and only a generated key can unlock the data with the exact combination, which is described as making it impossible for third parties to see what is inside the storage volume.
The article highlights new details from Microsoft spokesperson Charles Chamberlayne, who confirmed to The Verge that every BitLocker key generated for local device usage is also stored in Microsoft’s online storage server. Chamberlayne stated that customers can choose to store their encryption keys locally, in a location inaccessible to Microsoft, or in Microsoft’s cloud. He added that Microsoft recognizes that some customers prefer Microsoft’s cloud storage so the company can help recover their encryption key if needed and noted that while key recovery offers convenience, it also carries a risk of unwanted access.
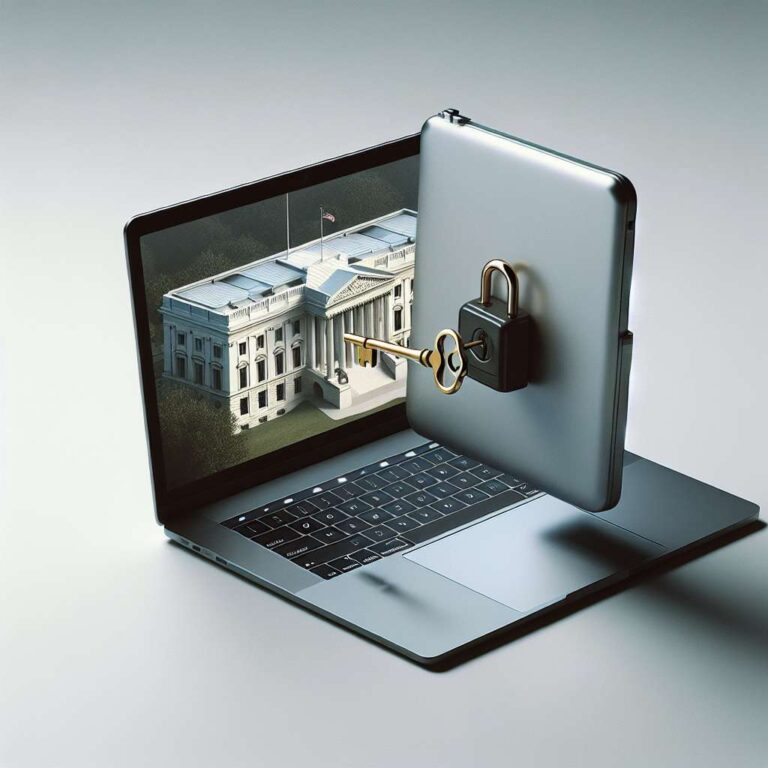
The report frames the revelation as a significant security and privacy concern because having these encryption keys stored online introduces what it calls a massive security vulnerability. The article argues that personal privacy can be circumvented in cases where a government body like the FBI requests access to the keys, since Microsoft can retrieve them from its servers. It portrays the situation as an inherent trade off between the convenience of cloud based recovery and the exposure to potential government demands or other unwanted access to encrypted data.